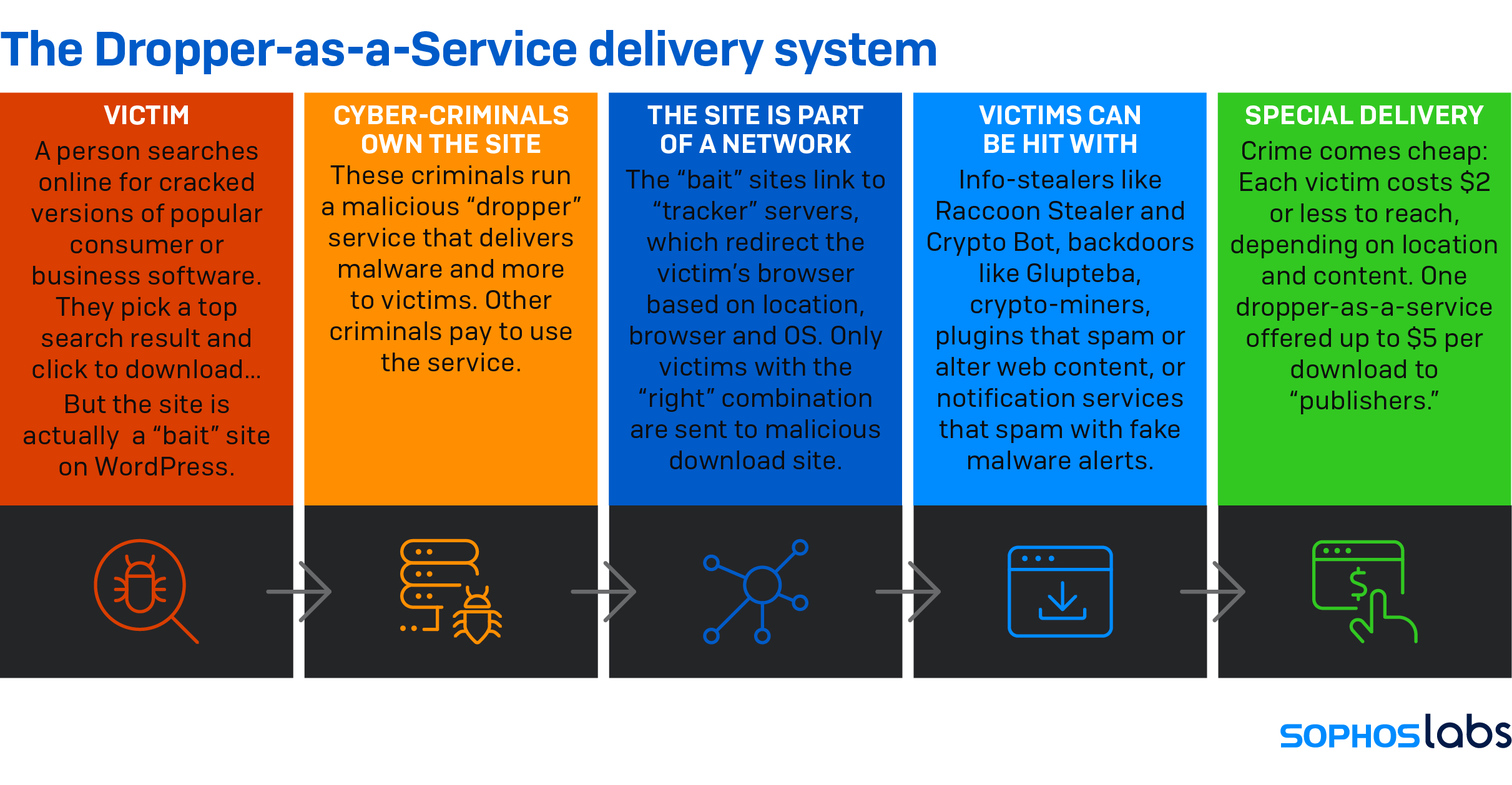
Sophos has released a new research, “Fake Pirated Software Serves Up Malware Droppers as a Service,” detailing how droppers for hire are delivering bundles of malicious and unwanted content to targets looking for “cracked” versions of popular business and consumer applications.
Sean Gallagher, Senior Threat Researcher at Sophos, said, “Paid download and dropper services have been around for a long time, but they continue to evolve and thrive and make money for the operators behind them. Our research suggests that this success is due in part to the fact that underground demand for account access credentials remains high, and these paid-for services enable less-skilled cybercriminals to implement bulk credential theft and cryptocurrency fraud at minimal cost.
“The dropper-as-a-service operators have also adapted to maximize their profits by bundling a range of malicious or unwanted content in each dropper, hitting victims with a raft of toxic applications in a single download.”
According to Gallagher, the last 18 months have seen millions more people working from home and often using personal devices to do that work. This has extended the risk of malicious dropper downloads to businesses and brought potentially far more lucrative corporate targets within the range of entry-level adversaries.
“For instance, our research uncovered droppers delivering backdoors such as Glupteba alongside information stealers such as Raccoon Stealer and Crypto Bot.
“Fortunately, when it comes to organizational security, malware delivered by droppers is easily detectable by security software, either because of its signature or its behavior. However, because malicious packages are in encrypted archives, security technologies don’t detect the malicious files until they are unpacked.”
SophosLabs recently published research into the Raccoon Stealer information stealer, which was delivered to targets as part of a malicious bundle by a dropper-as-a-service. In a follow up to this research, SophosLabs researchers have analyzed how these dropper services deliver their multiple payloads.
Below is a diagram of what happens when someone clicks to download what they think is pirated software, but which is, in fact, a disguised malware dropper:
InstallUSD is an example of a dropper-as-a-service, and its dropper infrastructure works as follows:
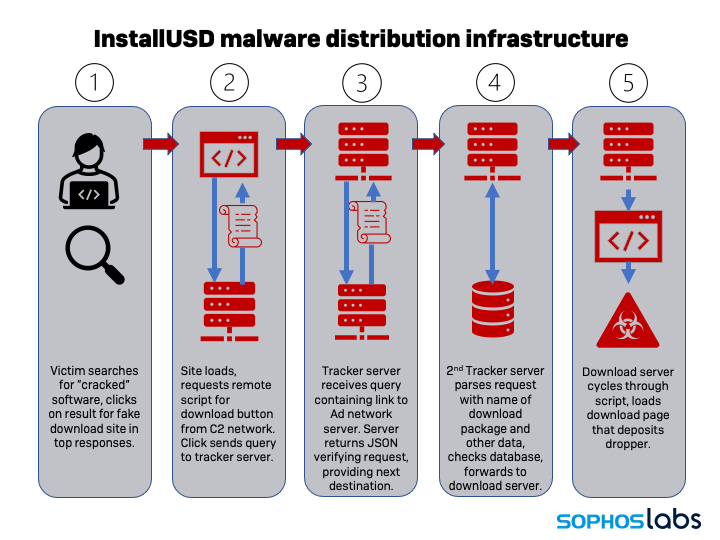
Further technical details on InstallUSD are available in the research blogpost on SophosLabs Uncut.
How to defend against droppers
Sophos recommends that organisations review their security software, settings and policies to ensure they can detect and block malicious and unwanted downloads.
This includes having a robust approach to web filtering. The malware hidden inside a dropper package may only be detectable once it is unpacked and by then it could already be inside the
network. A good web filter will not only scan regular downloads, but also inspect encrypted network traffic. According to Sophos research, more than half of malware now use Transport Layer Security (TLS) encryption for communications. Web filters also protect organizations and its employees from connecting to dangerous or untrustworthy servers in the first place, by blocking bad domains and URLs.
Organizations should complement network security with up-to-date endpoint protection that has behavioral detection capabilities on all of the devices that employees use to remotely access work-related services.










Discussion about this post