Group-IB has attributed a recent wave of scams impersonating UAE public bodies to a Chinese-speaking phishing gang, codenamed PostalFurious. The threat actor, documented for the first time by Group-IB in April 2023, has been targeting users in the Asia-Pacific by impersonating postal brands and toll operators. Now, Group-IB can confirm that the group has extended its operations to the UAE.
In early May, UAE authorities warned the country’s residents about a scam campaign that saw threat actors impersonate a local road toll operator. Group-IB’s Digital Crime Resistance Center in Dubai was able to attribute this campaign to PostalFurious, along with a second scam scheme that targeted UAE residents under the guise of a postal service. As part of its commitment to fighting cybercrime, Group-IB has shared its findings on the group with the Dubai Police Force and issued notifications for the impersonated brands.
Make it a double
In the aforementioned fake toll payment scheme, UAE residents receive fake messages asking them to urgently pay a vehicle trip fee to avoid additional fines. The text messages contain a shortened URL to obscure the true phishing address. Once a user clicks on the link, they are redirected to a fake branded payment page.
Figure 1: Fake payment page impersonating a road-toll operator. Source: Group-IB
The scammers’ goal is to compromise users’ payment data. According to Group-IB’s cyber investigations team, the campaign has been active since at least April 15, 2023.
Upon closer examination of the phishing infrastructure, Group-IB investigators found an almost identical scam campaign launched on April 29, 2023. The scammers used the same servers to host another network of phishing websites. The only difference between the two scam campaigns, which commenced two weeks apart, is the impersonated brand. In the latter campaign, scammers mimicked a UAE postal operator.
The latest scam wave also relies on smishing (SMS phishing) to deliver phishing links. The text messages were sent from phone numbers registered in Malaysia and Thailand, as well as via email addresses through iMessage. While it is unknown how many individuals were targeted in this campaign, Group-IB experts found that customers of multiple UAE telecommunications companies received rogue SMS messages.
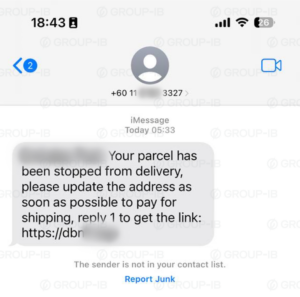
Figure 2: Fake SMS impersonating one of the country’s postal service providers. Source: Group-IB.
The URLs from the texts lead to fake branded payment pages that ask for personal details, such as name, address, and credit card information. The phishing pages appropriate the official name and logo of the impersonated postal service provider.
Group-IB experts note that the identified phishing websites utilise access-control techniques to avoid automated detection and blocking. The pages can only be accessed from UAE-based IP addresses.
Too Fast Too Furious
Group-IB’s cyber investigators, who regularly assist in INTERPOL-led operations in the MEA region, attributed both campaigns to a Chinese-speaking phishing ring dubbed PostalFurious.
PostalFurious, codenamed by Group-IB’s cyber investigations unit in early 2023, has been active since at least 2021. The name was drawn from the group’s decision to impersonate postal brands as well as their ability to quickly set up large network infrastructures, which they also change quite frequently to avoid detection by security tools.
The phishing resources for both UAE campaigns were hosted on identical web servers and their fake payment pages had the same design. The infrastructure behind these two scam schemes also shared many elements and code that were observed in previously analysed PostalFurious campaigns targeting the APAC region. In attacks targeting both the UAE and APAC markets, Laravel is used as an administration panel. The source code of the phishing sites targeting the affected UAE bodies contained comments written in simplified Chinese, which has previously been seen by Group-IB researchers during their prior research into PostalFurious.
Group-IB researchers underline that PostalFurious registers new phishing domains every day to rapidly expand their reach.
“Phishers are becoming more prolific and elaborate,” says Anna Yurtaeva, Senior Cyber Investigation Specialist at Group-IB’s Digital Crime Resistance Center in Dubai. “They can no longer be detected and stopped by automated blocking. People should stay vigilant and aware of ongoing scams. PostalFurious operations demonstrate the transnational nature of organised cybercrime and emphasise the need for a coordinated joint response that involves the general public, private sector, and government.”
How not to get scammed
Ensuring strong digital hygiene practices and exercising vigilance while online is crucial in preventing phishing and scams. Phishing emails or SMS messages often mimic legitimate messages from banks, credit card companies, or other organisations. It is essential not to rush into submitting your personal information. Find the company’s official website, look for reviews, and call customer support. An extra handful of seconds to double-check the URL or page name could make all the difference. If the website is demanding too much personal information, especially credit card information, be sure to ask yourself whether it is truly necessary.
Scammers usually impersonate legitimate brands. Brand owners should proactively monitor for and block scam and phishing websites upon detection. Group-IB’s Digital Risk Protection solution, part of the Unified Risk Platform, can reveal fraudulent infrastructure at early stages and initiate the takedown process.
The most effective way to stop cybercrime is to identify the perpetrators and bring them to justice. Group-IB’s Cyber Investigations team has conducted over 1,200 successful investigations all around the world helping private companies and international law enforcement organisations to combat advanced digital crimes.










Discussion about this post